Ukraine conflict: Digital and cyber aspects
Digital technology plays an important, if not decisive, role in the Ukraine-Russia conflict. Cyberattacks increase as the conflict escalates. Decisions by Big Tech and social media platforms about the services they provide or block directly impact the situation on the ground. Emerging technologies, such as cryptocurrencies, find new applications. Sanctions will impact the development of technology and e-commerce.
This page provides updates about the effects of the Ukraine-Russia conflict on cyber activities and digital networks – and vice-versa – including attacks on digital and critical infrastructures, access to the internet, the trade of technologies, the digital economy, and the use of cryptocurrency in the context of conflict.
Timeline of developments
Cyberattacks during the conflict
The war in Ukraine started on different levels – on the ground and likewise in cyberspace. On 23 February, the day before Russia's invasion of Ukraine, cyberweapons became a prelude to all-out war. Computer systems in different Ukrainian ministries, government organisations, and banks were the targets of distributed denial of service (DDoS) attacks. Researchers reported wiper attacks that erase the entire hard drive, usually making the whole system inoperable.
The current political climate presents a high possibility for cyberattacks to get out of control and escalate beyond the conflict in Ukraine. Some countries have already expressed their concerns about possible cyberattacks targeting their national critical infrastructures. And there are several possible scenarios for escalations to occur in the near future.
Russia, in line with its aggressive decision to put its nuclear forces on high alert, might respond with devastating cyberattacks. On the other hand, NATO has already confirmed that a cyberattack against any of its members would trigger Article 5 of the NATO Charter, allowing NATO to strike back with all means available. In the past, the USA and its allies have primarily resorted to public attribution of attacks to Russia and, eventually, some sanctions against the individuals involved. With their portfolio of sanctions now almost completely deployed already, there is not much more that they could do to respond economically to such attacks – so counter cyberattacks are a possible option.
However, both parties (Russia and Ukraine) in the conflict are signatories to most important international cyber agreements, which demand that specific norms be respected in cyberspace.
Cyberattacks and disinformation strategies play an integral part in the conflict. Besides states and their affiliated cyber proxies, various cyber groups and cyber gangs are taking sides as well, increasing the risk of escalation.
What is (not) allowed in a cyberconflict?
There are several major cyber agreements in the UN that both Russia and Ukraine have endorsed, which create an (voluntary) international framework of responsible state behaviour in cyberspace. This framework:
- confirms that international law, including the UN Charter, applies to cyberspace
- confirms that international humanitarian law applies, but only in situations of armed conflict
- outlines a number of voluntary cyber norms that states should adhere to
UN cyber-norms
Image source: ASPI
The framework of responsible state behaviour is defined by the final reports of the UN Open-ended Working Group (OEWG) and the UN Group of Governmental Experts (GGE) – all subsequently adopted by the UN General Assembly (UNGA).
In addition, participating states of the Organization for Security and Co-operation in Europe (OSCE) – including Russia, Ukraine, Belarus, the USA, and other European countries – have agreed on a set of voluntary confidence-building measures (CBMs). CBMs include consultations to reduce the risks of misperception, escalation, and conflict, and to using the OSCE as a platform for dialogue.
Evolution of international cybersecurity norms and negotiations
For more information about the UN GGE and OEWG, and cybersecurity processes, visit the dedicated Digital Watch page.
How can you protect yourself better from cyberattacks?
The US Cybersecurity and Infrastructure Security Agency (CISA) suggests measures to reduce the likelihood of damage from cyberattacks such as:
- implementing multifactor authentication for remote systems
- updating software, prioritising updates that address known vulnerabilities
- disabling ports and access points that are not essential for business purposes
- implementing strong controls for cloud services to avoid the risk of compromise
Tech sanctions
In response to Russia’s military operations in Ukraine, several countries have announced economic restrictions. According to the White House, over 30 countries representing well over half the world’s economy have announced sanctions and export controls targeting Russia. Russian Foreign Minister Sergei Lavrov has described the sanctions on Russia as ‘a tax on its independence’.
Unlike financial sanctions, which have an immediate impact on the economy, export controls on technology products will be felt over time. Cloud computing centres, high-performance computers, aviation and defence technologies, and oil-refining machinery all require regular replacements and upgrades of microprocessors, controllers, sensors, and mechanical parts. A lack of access to these technologies may set back the Russian economy and also weaken Russia’s military capabilities in the long term. In parallel, it could also accelerate a ‘balkanization of technology as Russia, like China, seeks independence from the West’.
USA sanctions
The USA has announced economic restrictions on 21 February, initially targeted at certain regions in the Ukrainian territory. Broad export controls and financial sanctions targeting Russia followed on 24 February, aiming to ‘choke off Russia’s import of technological goods’. The measures are being carried out by the US Department of Commerce’s Bureau of Industry and Security (BIS) and the US Department of the Treasury’s Office of Foreign Assets Control (OFAC).
Export controls introduced by BIS do not only aim to restrict Russian imports of defence, aviation, and maritime-related technology. They also impose restrictions on access to microelectronics, telecommunications items, sensors, and navigation equipment, which were previously not submitted to export controls. The measures will halt direct exports from the USA to Russia, and will also affect technological products that are manufactured outside the USA, which use American equipment or technology, i.e. machinery, software or blueprints.
BIS’ export controls measures against Russia were taken under the authority of the Export Control Reform Act of 2018 and its implementing regulations, the Export Administration Regulations (EAR). Changes introduced by the measures include:
- Imposing the new Commerce Control List (CCL)-based licence requirements which include categories 3 to 9 of the CCL, encompassing computers, telecommunications, and information security, among others.
- Implementing a ‘policy of denial’ to licence applications for exports, re-exports, and transfers of restricted technologies. This means that any exceptions to ongoing restrictions will be reviewed on a case-by-case basis, and licences will be granted only in specific and rare cases, i.e. humanitarian needs, civil telecommunications infrastructure, safety of flight, maritime safety, government space cooperation.
- Expanding the existing Russian ‘military end use’ and ‘military end user’ control scope to all items subject to the EAR, with the exception of food, medicine, and a few other items, as long as they are not for Russian ‘government end users’ or Russian state-owned enterprises.
- Adding new foreign direct product (FDP) rules specific to Russia and Russian ‘military end users.’ These rules have a broad scope of application, and will allow control over foreign-produced items that are either the direct or indirect product of US software or technology subject to the EAR. The rules also create more extensive control over FDP for actors which are considered ‘Russian military end users’ according to the US Entity List in Supplement No. 4 to Part 744 of the EAR.
- Adding 49 entities to the list of ‘Russian military end users’ under the Entity List footnote 3. Russia military end user FDP rules will apply to these entities. A licence will be required to export, re-export, and transfer (in-country) all items subject to the EAR to these entities, with limited exceptions. Exceptions will be considered according to the ‘policy of denial’ mentioned above.
On 2 March, similarly stringent export control restrictions were imposed on Belarus by BIS, in response to its ‘substantial enabling of Russia’s further invasion of Ukraine’.
The White House estimates that ‘severe and sustained controls will cut off Russia’s access to cutting edge technology, contributing to undermine Putin’s ability to project power’. Among analysts, views are split on the impact of the export restrictions on access to technology. While some believe that the measure will have ‘a real, significant impact on these sectors of the Russian economy for many years’, others remarked that Russia ‘is not a significant direct consumer of chips or of information technology equipment’.
The US Department of the Treasury’s OFAC is also engaged in the application of sanctions on financial services. OFAC prohibited US persons from engaging in transactions with the Central Bank of the Russian Federation, the National Wealth Fund of the Russian Federation, and the Ministry of Finance of the Russian Federation (Directive 4 under Executive Order 14024). According to the Specially Designated Nationals List Update, OFAC also sanctioned the Russian Direct Investment Fund (RDIF) and its Chief Executive Officer (CEO), Kirill Dmitriev, considered a key ally of the Russian government.
EU sanctions
During a meeting on 24 February, the European Council agreed on imposing sanctions covering the financial sector, the technology sector, the energy and transport sectors, dual-use goods, export control and export financing, and visa policy. A package of sanctions was approved on 25 February, aiming to ‘cut off Russia’s industry from the technologies desperately needed today to build a future’, according to Commission President Ursula von der Leyen.
The restrictions introduced by Council Regulation (EU) 2022/328 impose a blanket ban on the supply of dual-use items to any Russian person or for use in Russia (article 2). Dual-use items refer to goods, software, and technology that can be used for both civilian and military applications (listed in Annex I to Regulation (EU) 2021/821). The sanctions also include standard prohibitions on providing technical assistance, brokering, and other services related to dual-use items, and on providing related financing or financial assistance.
Regulation 2022/328 also prohibits the export of a wide variety of goods and technology beyond the dual-use list, which might contribute to Russia’s technological enhancement of its defence and security sector (article 2a). These items are listed under annex IV and include electronic devices (ex. semiconductors), computers, telecommunications equipment, information security, sensors, and lasers, among others.
A new set of measures approved by the Council of the EU on 28 February adopt restrictions related to aviation and finance, introducing a prohibition to make transactions with the Russian Central Bank. The council also introduced economic sanctions against 26 persons and 1 entity which include freezing of assets.
In addition, the European Parliament called for the export of any high-tech products and strategic goods to the Russian market to be banned, and called the EU and the Member States to terminate the software licences for military and civilian equipment in Russia and Belarus, especially those used for communication and satellite navigation.
Russian countermeasures
As a countermeasure to Western tech sanctions over the conflict in Ukraine, the Russian Government adopted a decree which allows local companies and individuals to use inventions, utility models, and industrial designs held by owners from ‘unfriendly countries’ without their consent and without paying compensation. The list of unfriendly countries includes the USA, Canada, the EU, the UK, Ukraine, Switzerland, Japan, South Korea, Australia, New Zealand, Singapore, and Taiwan. The decree relies on provisions in the Russian Civil Code, which authorises the government to waive patent owners’ consent in the case of extreme necessity associated with supporting the defense and safety of the state, and the protection of citizens’ life and health.
Analysts point out that the decision could be interpreted as a countermove against Western tech companies, such as Google, Apple, and Microsoft, which are among the firms that announced a revamp of their business plans in Russia amid the Russia-Ukraine conflict. The Russian government is also considering the introduction of a compulsory licensing mechanism for computer programs and databases, according to a proposal called the ‘Priority Action Plan for Ensuring the Development of the Russian Economy in the Conditions of External Sanctions Pressure’ (English translation) by the Russian Ministry of Economic Development. The proposal lays out numerous policies that attempt to help stabilize the Russian economy.
SWIFT
Economic measures have also been jointly imposed by the European Commission, France, Germany, Italy, the UK, Canada, and the USA. The signatories decided to exclude some Russian banks from SWIFT (Society for Worldwide Interbank Financial Telecommunication), a Belgium-based network of 11,000 banks from 200 countries and territories that implements an international payment system used by thousands of financial institutions. SWIFT is also the organisation designated by the International Organization for Standardization (ISO) to assign Business Identifier Codes (BIC), which uniquely identify member organisations within the messaging system.
SWIFT-related sanctions are intended to interfere with Russian economic activities. It is not clear if these measures could result in disruption of Russian gas and oil supplies, but they have already caused problems for Russian customers, who have been unable to use mobile payment apps, such as Apple Pay or Google Pay or make online payments to countries that issued these sanctions.
SWIFT has confirmed that it will disconnect seven designated Russian entities (and their designated Russia-based subsidiaries) under EU sanctions on March 12 from the international payment system.
Some analysts point out that removing Russian banks from SWIFT may have negative consequences on global governance by making rule-based international institutions ‘arbitrary and unpredictable tools of geopolitical rivalry’. Governments’ legitimacy to request a private network to implement their policy objectives remains unclear. There is also a lack of redress mechanisms for affected Russian banks if they wish to appeal the decision.
Digital economy
The conflict in Ukraine may have a far-reaching impact on the digital economy, as it could exacerbate the current chip shortage, which has led to significant financial losses across several sectors, from computers to carmakers in recent years. Some raw materials exported from Russia and Ukraine, such as palladium, nickel, platinum, rhodium, and titanium, as well as gas neon and chemical C4F6 are critical for semiconductor manufacturing. Ukraine supplies more than 90% of the neon consumed by the United States, while Russia supplies 35% of the US’s palladium. The conflict could lead to supply chain disruption, the rapid depletion of inventories, and increasing prices.
The conflict could also affect the availability of online payment methods. Visa, Mastercard, and American Express suspended their operations in Russia. The move was welcomed by the White House, but the impact on the national economy may not be so significant since customers in Russia will be able to continue using the cards until they expire. The most immediate consequence will be that transactions initiated with cards issued in Russia will no longer work outside of the country, and any cards issued outside of Russia will no longer work within the country. To mitigate these consequences, Russia will likely start a transition towards the Chinese system UnionPay, which is already accepted around the world, although not as widely as Visa and Mastercard. PayPal also suspended activities in Russia. In the present situation, it is ‘basically impossible to send money to any individual in Russia’ according to some analysts.
These decisions raised concern among activists and independent journalists, who will be unable to send their resources abroad and might be more tightly controlled by the Russian government.
Cryptocurrencies and war economy
'Because there is no central controller who can impose their morals on its user, crypto can be used to crowdfund for the Ukrainian army or help Russia evade sanctions.'
Tom Robinson, Chief scientist and co-founder of crypto analytics firm Elliptic (Source: The Washington Post))
Cryptocurrencies became an important factor in the Ukrainian conflict. They are increasingly used by both sides trying to overcome financial hurdles in the region. The Ukrainian banking system is not functioning for most of the country, while Russia is still expected to feel the full impact of the removal from the SWIFT.
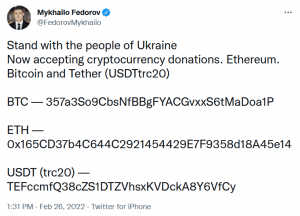
In retrospect, Ukraine was on the technology forefront regarding cryptocurrency development. Many Ukrainian developers work in the FinTech and crypto industry. Back in 2021, Ukraine introduced regulation of digital assets, recognising bitcoin and other cryptocurrencies. There have been many reports about the GoFundMe type of crowdsourcing campaigns in which people sent cryptocurrencies to help the Ukrainian fight. Ukraine’s Minister of Digital Transformation Mykhailo Fedorov posted the addresses of official cryptocurrency wallets the Ukrainian government will manage on Twitter. Listed wallets are for bitcoin, ether, and tether cryptocurrencies.
On 1 March, the ministry announced support from two more major cryptocurrency projects: Solana and PolkaDot, which will enable donations made in Sol and Dot cryptocurrencies.
First estimates on funds gathered in cryptocurrency came from the official Ukranian Twitter account, announcing US$33 million were collected in the first week. Furthermore, the Ukrainian Minister for Digital Transformation, announced the launch of NFT products to continue fundraising efforts.
People who were forced to find refuge in neighbouring countries could not access their bank accounts. Forced to escape with a handful of cash, people with digital assets could access them all the time, and use them in another country. This proved that global digital assets represent a great form of transboundary value in times of crisis.
On the other hand, Russia was prominently opposed to cryptocurrencies. Yet in a sudden turn of events, it has pushed a draft proposal for a central bank digital currency (CBDC) and regulation of other digital assets such as bitcoin and ether, recognising the crypto mining industry and crypto-exchanges. The draft law was in front of the parliament only a couple of days prior to the conflict. There is still some discrepancy between the Russian Central Bank, which stands to continue to ban all cryptocurrencies, and the Russian government which is pushing for a more relaxed approach.
The adoption of the regulation will also create the regulatory framework for Russia’s bitcoin mining industry. The industry became significantly larger in 2021 after China decided to close down crypto mining facilities in their country. By some estimates, the Russian cryptocurrency mining industry is valued at US$140 billion, and it is unaffected by the current crisis.
While under a strict financial embargo from the rest of the world, Russia might turn to the cryptocurrency payment system with other states. During the past couple of years governments of Venezuela, Iran, and India looked for successful ways to make transactions outside of the current global finance system. So far, none of it resulted in any prolonged practices.
In the 'war economy', cryptocurrencies can be used for circumventing strict sanctions on the banking system, crowdfunding, and other financial activities. The US government is working to implement more regulations, in particular regarding sanction regimes. The US Department of the Treasury issued guidelines to cryptocurrency operators requesting that they observe the rules and regulations of the platforms they operate on.
Starlink and Internet access
Elon Musk announced internet access provided by SpaceX's Starlink Service as a response to severe disruptions in internet service in Ukraine during the Russian invasion.
SpaceX's Starlink services offer broadband internet access via a constellation consisting of approximately 2,000 satellites that orbit low in the Earth's orbit. Starlink should be able to provide internet access to any place on Earth.