Cybersecurity
The vulnerability of the internet is the vulnerability of modern society. However, security has mostly been an afterthought since the early days of the internet as many market-driven tech companies employed a ‘release now, patch later’ approach.
The growing use of cyberspace by state and non-state actors for malicious purposes threatens peace and security, trust in the digital economy and services, and the potential for the digital transformation of societies and economies. Security risks for citizens, companies, and countries are interrelated.
Vulnerabilities used by criminals can easily slide into a military arsenal and vice versa. Thus, effective digital security requires a holistic approach to better tackle the interplays between security, economic development, human rights, as well as sociocultural and infrastructural aspects. Cybersecurity is the main umbrella public policy issue. Other more specific security-related issue include:

Child safety online
Are you concerned about the safety of your child in the digital age? Learn the risks and challenges of keeping children from cyberbullying, inappropriate content, and other online threats....
Critical infrastructure
Did you know that cyberattacks on critical infrastructure can have devastating consequences? Discover how governments, private sectors, and international organizations are working together to ensure the security of our infrastructure....
Cyberconflict and warfare
Are you aware of the potential risks of cyberconflict in today's digital age? With the world becoming increasingly digitalised, the stakes have never been higher. Explore our page to learn how cyber operations can be used as a tool for political and military purposes, what implications this can have on global security, and the international norms and laws governing them....

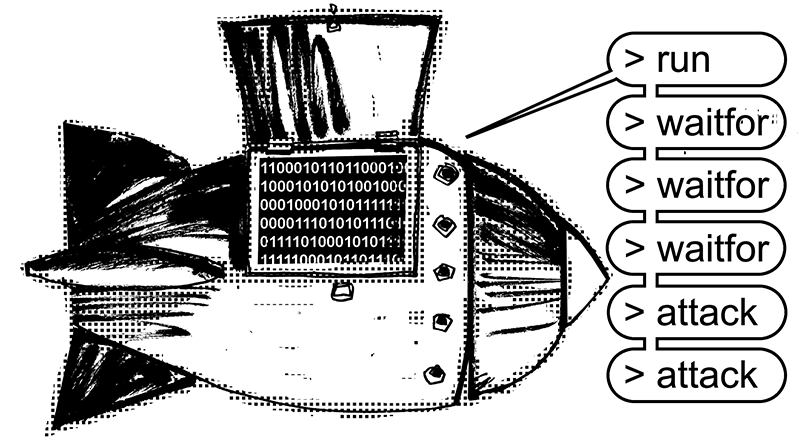
Cybercrime
Have you ever wondered how cybercrime is impacting our digital world? Find out the latest insights and trends on cybercrime! Learn how cybercriminals operate and what measures are being taken to combat them. Stay informed and stay safe online!...
Encryption
Is encryption a boon or a bane for digital security? Get a comprehensive overview of the encryption debate! Learn about the benefits and challenges of encryption and how governments and law enforcement agencies are trying to balance security and privacy concerns....
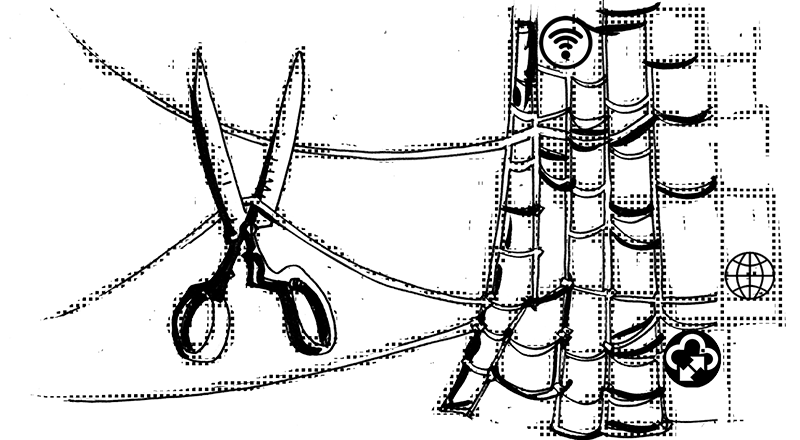
Network security
How can we ensure the security and resilience of our digital networks? Learn about the emerging threats and challenges faced by digital networks and how governments, businesses, and individuals can work together to secure our networks against cyber threats....

Violent extremism
How can the internet be used as a platform for spreading violent extremism? Discover the latest research and analysis on the intersection of violent extremism and the online world. Learn how extremist groups use social media and other online platforms to recruit members and spread their message....
